How to Repair a WordPress Database

The WordPress database holds every post, page, user account, setting, plugin option, and comment; when that database goes corrupt, the site stops behaving like a site. Five methods recover a corrupted WordPress database across the surfaces most WordPress administrators actually reach for: the WP_ALLOW_REPAIR maintenance page, phpMyAdmin, WP-CLI, a hosting control panel’s database tool, and a dedicated repair plugin.
A reliable recovery runs as a sequence: diagnose the corruption by recognizing the signals before anything is touched, understand the cause that produced it, back up the database immediately beforehand, select a method that matches the access available and the severity at hand, execute the repair, and verify that the database returned to a functional state once the operation completes.
On a live site, the same sequence operates under a tighter discipline, such as staging-first execution, an audit trail alongside the work, and a clear handoff point when production infrastructure is not in place. A repair that ignores the cause can invite the same failure a week later, and every repair carries a measurable risk on a badly damaged table; the REPAIR TABLE truncation scenario is the concrete one, which is why the backup step is non-negotiable.
The WordPress database sits inside a small cluster of sibling operations that read as a triad. The definition of a WordPress database, such as what tables it holds, how WordPress reads and writes them, and how MySQL or MariaDB stores them. WordPress database backup copies the database to a safe location, runs before any repair, and is covered in the separate WordPress database backup guide.
WordPress database optimization is the routine maintenance operation that trims overhead, reorganizes indexes, and reclaims storage on a healthy database, and is covered in the separate WordPress database optimization guide. Backup and optimization are distinct procedures from repair at the operation layer; the definition sibling is the entity foundation under all three.
What WordPress Database Repair Is
WordPress database repair is the recovery procedure applied to the MySQL or MariaDB database that holds a WordPress site’s tables, run to return a corrupted database to a functional state. The repair operation works at the table level, including table headers, indexes, or row data that the database engine flags as damaged, and executes through two classes of surface.
WordPress-native surfaces carry repair through the CMS: the WP_ALLOW_REPAIR constant exposes a maintenance-page repair tool, the WP-CLI command wp db repair runs the same table-level repair from the shell, a hosting control panel bundles a repair action into its database tool, and a repair plugin drives the same mechanism from inside wp-admin.
Database-native surfaces carry repair directly against the engine, below WordPress: phpMyAdmin exposes a Repair table action on a selection, the mysqlcheck utility runs repairs in batch from the command line, and the REPAIR TABLE SQL statement runs the operation table by table in a database client.
The engine layer shapes what “repair” can actually do. Classic MyISAM tables support the full REPAIR TABLE operation, such as the engine rebuilding an index, reconstructing a header, or recovering what it can from damaged rows. InnoDB, the storage engine WordPress defaults to on modern MySQL and MariaDB installations, does not respond to REPAIR TABLE in the same way; InnoDB handles most corruption through its own recovery modes (the innodb_force_recovery setting) or, in harder cases, through restoration from a backup.
Identifying which engine a given table uses is part of identifying which repair path will reach it; the engine check is a fixed property of the repair operation, regardless of which method drives it.
WordPress database repair is also delimited by what it is not.
Three sibling procedures sit at the same operation layer: defining the database (understanding what the database is and how WordPress uses it), backing it up (copying the database to a safe location), and optimizing it (maintenance on a healthy database); each is covered in its own guide and is not part of WordPress database repair. Where a tool exposes both Repair and Optimize (phpMyAdmin, the WP_ALLOW_REPAIR maintenance page, practitioner repair plugins), the repair path is the only one that belongs to WordPress database repair.
Then there is the wider term. WordPress repair, in its broader sense, covers the full spread of WordPress-site breakage, including file-level damage from a failed upload, theme conflicts that white-screen the front end, plugin conflicts that crash the admin area, permissions problems, PHP version mismatches, and .htaccess regressions. Those repairs happen against files, configurations, and code, not against the database.
WordPress database repair differs from WordPress repair in exactly that way: the database layer, not the file, theme, or plugin layers. The broader territory is valid and has its own playbooks, but none fall within WordPress database repair. WordPress database repair defined, the administrator’s first operational move is recognizing when a WordPress database has actually gone corrupt.
How to Diagnose WordPress Database Corruption
Diagnose WordPress database corruption by checking three signals at three layers of the stack: the WordPress application layer, the database engine layer, and the storage or host layer. Any one of the three may be the signal the administrator sees first. Recognition is the gating decision before any repair work begins; running a repair against a database that is not corrupt, or against one whose problem is not table-level damage at all, wastes time and can make things worse. Three patterns cover most real incidents.
The Error establishing database connection message is the most common and the most unambiguous signal. It appears at the top of the page where the WordPress site used to render, served by the CMS itself after a failed attempt to reach the database. The message means WordPress cannot open a connection at all, either the database server is refusing the connection, the credentials in wp-config.php are no longer valid, or the database the connection opens into has corruption, severe enough to fail the handshake.
Once credentials and server reachability are confirmed (a short check against the hosting control panel or a ping of the database host), a persisting Error establishing a database connection points to corruption at the database itself, and the signal is a repair candidate.
The White Screen of Death, from a database-corruption point of view, is a subtler pattern where the database cause sits one layer down. The front end, the admin area, or both render as a blank white page with no error message, no content, and no theme visible. The mechanism is a PHP fatal error triggered by a failed database query: WordPress queries the database, the query returns an error or a malformed result, PHP fatals on the unexpected response, and the page dies without writing output.
Enabling WP_DEBUG in wp-config.php surfaces the underlying error, and when the surfaced message names a table, a corrupted row, or a query that cannot complete, the blank page traces back to database corruption. The same White Screen of Death also appears for theme or plugin fatals unrelated to the database, so the diagnostic here is less about the blank screen and more about what the debug log reveals underneath it.
The third pattern surfaces from the database layer without depending on the WordPress UI to fail. The MySQL error log records what the engine sees, and it records corruption plainly: table-level errors, repair-needed flags on specific tables, InnoDB warnings about page checksums or damaged spaces, MyISAM index failures. The log path depends on the install; /var/log/mysql/error.log on many Linux hosts, a log viewer in cPanel or Plesk, a log tail through the hosting control panel on managed stacks, but the signal is the same wherever it lives.
A repair-needed flag against a WordPress table in the MySQL error log is often the earliest warning available, surfacing hours or days before the front end or admin area actually breaks. Administrators watching the log catch corruption before the site ever throws an Error establishing database connection message; administrators who check the log only after the site breaks use it as confirmation that corruption, not a credentials problem or a server outage, is the root cause.
Recognizing the pattern is half the diagnosis. The other half is understanding the conditions that produced the corruption, because a repair that ignores the cause tends to invite the same corruption back.
Common Causes of WordPress Database Corruption
WordPress database corruption has four common causes: server crash and incomplete writes, plugin conflict, storage engine fault, and disk failure. The four classes cover the four layers at which corruption can arise, such as server, application, storage engine, and hardware, which is what makes the set structurally exhaustive rather than merely a frequent-cases list. Server crashes and plugin conflicts produce the highest-frequency corruption; storage engine faults and disk failures produce lower-frequency but more severe corruption, with disk failure the most severe class.
- Server crash and incomplete writes: a write transaction halts mid-flight, leaving the on-disk state neither pre- nor post-transaction consistent.
- Plugin conflict: poorly written plugins issue malformed queries or manipulate core tables in ways the CMS cannot subsequently read.
- Storage engine fault: a damaged header, index, or page originates inside the storage engine at the table level.
- Disk failure: hardware-layer I/O errors propagate upward through the engine and surface as table corruption.
Server crash and incomplete writes are the most common cause class. A write transaction against the WordPress database is an in-flight operation: rows are being updated, an index is being rewritten, and a log page is being flushed. When the server loses power, the MySQL process is killed ungracefully, the container is terminated mid-request, or the virtual machine reboots under the operation, the write stops halfway.
What the database engine finds when it comes back up is a table whose on-disk state reflects neither the pre-transaction snapshot nor a completed post-transaction one. The header disagrees with the data file, an index disagrees with the rows it points at, or a page checksum fails because half the page was written and half was not. REPAIR TABLE was built for this class of corruption and addresses it most cleanly.
Plugin conflict is a WordPress-specific cause class and describes data inconsistency introduced at the application layer. A plugin conflict at the database layer is a state in which plugin code issues queries or writes that leave core or plugin tables in a state the CMS cannot subsequently read: malformed queries the engine accepts structurally, orphaned rows left behind when a plugin is deactivated or updated incorrectly, or values written to wp_posts, wp_options, or wp_postmeta through paths that break the CMS’s expectations (a serialised-array representation that becomes malformed, a charset mismatch on a multilingual field, a schema expectation the plugin violates in an update).
None of this is corruption in the engine-level sense of a damaged header or a failed page checksum, but it produces the same user-visible result: queries return errors, pages stop rendering, and the database needs remediation before the site recovers. The mechanism traces to the WordPress plugin ecosystem itself, which is why the problem surfaces on WordPress specifically and does not surface on a vanilla MySQL instance.
A storage engine fault is a table-level defect originating inside the storage engine, which is a damaged.MYI index file on a MyISAM table, a broken header the engine cannot parse, or a compressed-data fault on an ARCHIVE table. MyISAM and ARCHIVE are the table engines REPAIR TABLE was designed to handle; their table-level architecture makes a damaged header or a broken index recoverable at the engine’s own level. Corruption in a MyISAM.MYI index file or an ARCHIVE table’s compressed data surfaces as the clean table-level fault that the repair addresses most directly.
InnoDB, the default engine on contemporary WordPress installations, does not fault in the same way and does not recover through the same path; the InnoDB constraint returns as the hardest axis in method selection. A fault that originates inside the storage engine, at the table level, is one of the four cause classes and is the one REPAIR TABLE is designed to address.
Disk failure is a hardware-layer fault, such as a failing SSD, a degraded block on a SAN volume, or a filesystem issue on the host, that produces I/O errors propagating upward through the engine and surfacing as table corruption. It is the lowest-frequency cause class and the highest-severity one. Unlike a plugin conflict or a server crash, disk failure does not resolve itself when the write path is restored; it continues producing new corruption until the underlying hardware is replaced or the database is migrated to a healthy volume.
When the MySQL error log shows repair-needed flags reappearing after a clean repair, or when corruption spreads across tables that share no application logic, a hardware-layer cause is usually why. A repair can still recover the database in the short term, but on failing storage, the recovery is buying time, not addressing the root cause.
How often each pattern shows up is not the same as how to prevent it, and prevention is a different operational discipline. The four cause classes map an incident in front of the administrator to a probable cause, which in turn shapes how confident the administrator can be that a repair will hold against the same conditions recurring.
WordPress Database Backup Before Repair
Back up the WordPress database before running any repair method. The backup is the one non-negotiable step between diagnosis and execution, and no administrator should advance past it on a production site. A backup taken immediately before the repair is the rollback point, which is the single reliable way to return to a known state if the repair attempt worsens the corruption rather than resolving it. Understanding how to back up the database in WordPress is, therefore, a prerequisite.
The risk is concrete enough to justify the gate. REPAIR TABLE on a severely damaged MyISAM table where the engine cannot reconstruct rows, can truncate those rows, and a plugin-driven repair that misreads the corruption pattern can overwrite salvageable data with a partial repair that does not fully restore the data. Both outcomes are recoverable only from a fresh backup. A backup taken yesterday, or even an hour before the corruption symptoms first surfaced, may already be stale against whatever writes happened between then and the repair, which is why the prerequisite is specifically a pre-repair backup, not just the most recent scheduled backup.
A backup that satisfies the requirement takes one of several recognizable shapes: a full database dump produced with mysqldump, a structured export generated through phpMyAdmin, or a hosting-panel snapshot captured through the managed host’s own backup tool. Any of the three produces an artefact the database can be restored from if the repair goes wrong.
WordPress database backup as a procedure, which tool to reach for in which context, how to capture a consistent backup of a live site, how to verify a dump is restorable before trusting it, is covered in the separate WordPress database backup guide. The pre-repair backup is a prerequisite; the administrator arrives at the repair with a backup already taken, or captures one and returns.
With a pre-repair backup captured, the administrator maps access level, storage engine, and production constraint to the repair method that those three axes allow.
WordPress Database Repair Method Selection
Select a WordPress database repair method by mapping site-access level to the engine constraint and the production constraint. Five methods are available, including the WP_ALLOW_REPAIR maintenance page, phpMyAdmin, WP-CLI, a hosting control panel, and a repair plugin. Three selection axes narrow the choice: access level, storage engine, and production constraints. Each axis rules methods in or out for a given situation; together, they usually yield one or two candidates that the administrator can execute with confidence.
Access level is the first filter, and it asks a simple question: what surface can the practitioner actually reach? A site owner working from wp-admin with no shell or hosting-panel access has two methods available: the WP_ALLOW_REPAIR maintenance page, which lives inside WordPress itself, and a dedicated repair plugin, which wraps the same table-level repair behind a wp-admin UI. An administrator with SSH access to the hosting environment opens WP-CLI, which runs the repair from the command line without needing a browser session at all.
Hosting control panel access, including cPanel, Plesk, Runcloud, or the equivalent, opens the panel’s own database tool, which bundles a repair action alongside the standard database operations. phpMyAdmin usually sits next to panel access on shared hosts, reachable through a link in the control panel’s database section, and its selection-based Repair action is the repair surface that UI-level database access exposes. The surfaces do not overlap arbitrarily; each one favors a method, and the presence or absence of a surface determines which methods are in play at all.
The storage engine is the second filter, and it is the most technically load-bearing constraint in selection. REPAIR TABLE is the SQL statement that sits underneath phpMyAdmin’s Repair action, WP_ALLOW_REPAIR’s internal repair routine, WP-CLI’s wp db repair command, and most hosting-panel repair tools, and it works on MyISAM and ARCHIVE tables. It does not work on InnoDB. A WordPress site whose tables are entirely InnoDB (the default on any reasonably modern install) cannot be repaired through the paths that wrap REPAIR TABLE, and attempting to run them returns a note from the engine that the storage engine does not support the operation.
InnoDB corruption recovers through a different path; the innodb_force_recovery configuration setting, which brings the engine up in a restricted mode long enough to dump the data, or a restore from the pre-repair backup. The details of the InnoDB recovery path belong to a separate procedure; for selection, a site on InnoDB rules out four of the five repair methods for table-level damage and leaves restore-from-backup as the operative path. A mixed installation, such as MyISAM tables for a legacy plugin and InnoDB for everything else, threads the needle: REPAIR TABLE-based methods repair the MyISAM tables, and the InnoDB side is handled separately if it shows corruption.
Production constraint is the third filter, less about tooling than about when and how the method runs. A repair on a staging copy carries none of the risk a repair on a live site carries; the staging site can be rebuilt, rerun, or rolled back with no consequence beyond the practitioner’s own time. A repair on a live production site, by contrast, runs against the database the business is actively reading from and writing to, which can hold table locks briefly, cause downtime, and leave the site in worse shape if a half-completed operation is interrupted.
Live sites favor methods that complete quickly, hold locks briefly, and leave an auditable trail afterward. A plugin’s one-click action on a live site, by contrast, concentrates risk into a single unreviewable step. Access level determines which methods are even available to the administrator, while the production constraint reshapes which of those available methods the administrator reaches for when a live site is on the line.
The three axes, such as access level, storage engine, and production constraint, usually converge on one or two candidate methods, not a single answer. A site owner on shared hosting with InnoDB tables on a live site arrives at a different candidate than an administrator with SSH access to a staging copy of a legacy MyISAM database, and the difference is constraint-driven rather than opinion-driven. With constraints mapped to candidates, the administrator runs the selected method against the WordPress database.
How to Repair the WordPress Database
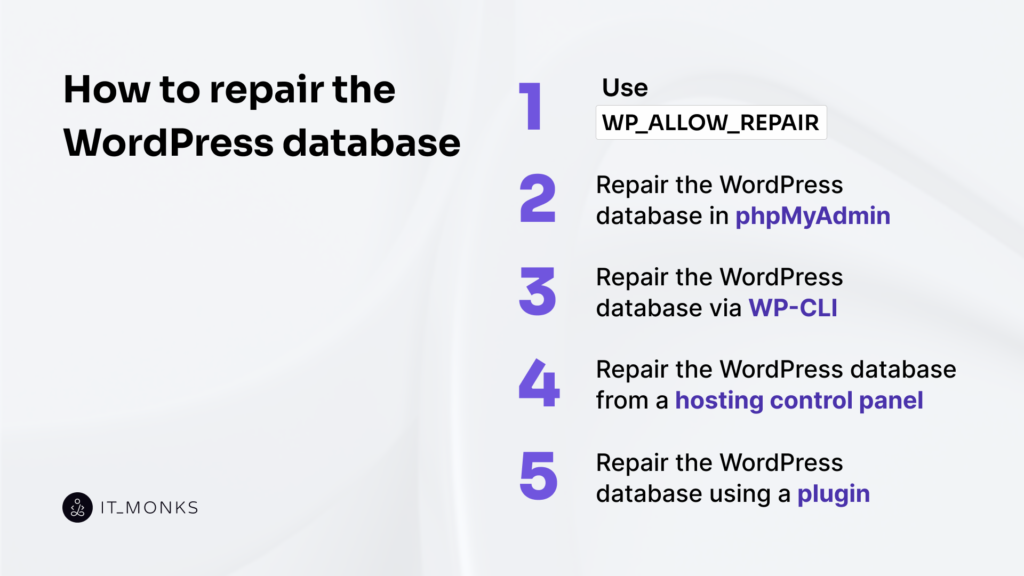
Five surfaces repair a WordPress database, including the WP_ALLOW_REPAIR maintenance page, phpMyAdmin, WP-CLI, a hosting control panel, and a dedicated repair plugin, each accessed at a different layer of the WordPress stack. WP_ALLOW_REPAIR lives inside the CMS and runs against the database from a maintenance page that any administrator with wp-config.php access can enable. phpMyAdmin sits at the database layer; a database-native UI that most shared, cPanel, and Plesk hosting expose, and runs the repair against the tables directly. WP-CLI is the shell-level path, available wherever SSH access is available, and runs the same table-level repair from the command line, often paired with routine WordPress database optimization tasks.
A hosting control panel, such as cPanel, Plesk, Runcloud, and their equivalents, wraps the operation behind a managed-host button. A dedicated repair plugin drives the same underlying mechanism from inside wp-admin for administrators who do not have anything below the WordPress layer to work from.
No method is ranked against the others. Each surface exists because some access level reaches it and the others do not, and the appropriate method is the one that the situation has already selected through the three filters, such as access level, storage engine, and production constraint.
The same REPAIR TABLE operation, or its functional equivalent on supported storage engines, runs underneath most of the five; the difference is which door the administrator walks through. WP_ALLOW_REPAIR is the built-in WordPress maintenance page that exposes a repair surface through a constant in wp-config.php, and phpMyAdmin is the database-native UI that exposes a Repair table action against selected tables.
Use WP_ALLOW_REPAIR
WP_ALLOW_REPAIR is the WordPress built-in repair surface, which is a constant that unlocks a maintenance page inside the CMS and runs the table-level repair against the WordPress database from there. It is the lowest-access starting point among the five methods: any administrator who can edit wp-config.php can enable it, no shell, no hosting panel, no database client required. The surface does two things: runs the repair, and while it is enabled, exposes that repair to anyone who knows the maintenance-page URL, and the administrator must handle both.
Enabling the surface is one line in wp-config.php. Add define(‘WP_ALLOW_REPAIR’, true); to the file, placed above the comment that reads “That’s all, stop editing! Happy publishing.” is the line WordPress uses as the conventional ceiling for user-added configuration, below which the file’s own bootstrap logic runs. The define signals to WordPress that the maintenance-page repair tool at /wp-admin/maint/repair.php should respond.
define('WP_ALLOW_REPAIR', true);With the definition in place, the repair run is a browser operation. Visit /wp-admin/maint/repair.php on the WordPress site; the path resolves to the maintenance page regardless of whether the administrator is logged in. The maintenance page presents two buttons. The first is Repair Database. The second is Repair and Optimize Database. Choose Repair Database.
The maintenance page runs the repair against every table in the WordPress database and prints a per-table status line as each completes, providing a short list the administrator can scan to see which tables need work and whether each operation returned cleanly. The Repair and Optimize Database option combines the repair with the optimize operation; the optimize half of that option is out of scope for repair and is covered in the separate WordPress database optimization guide.
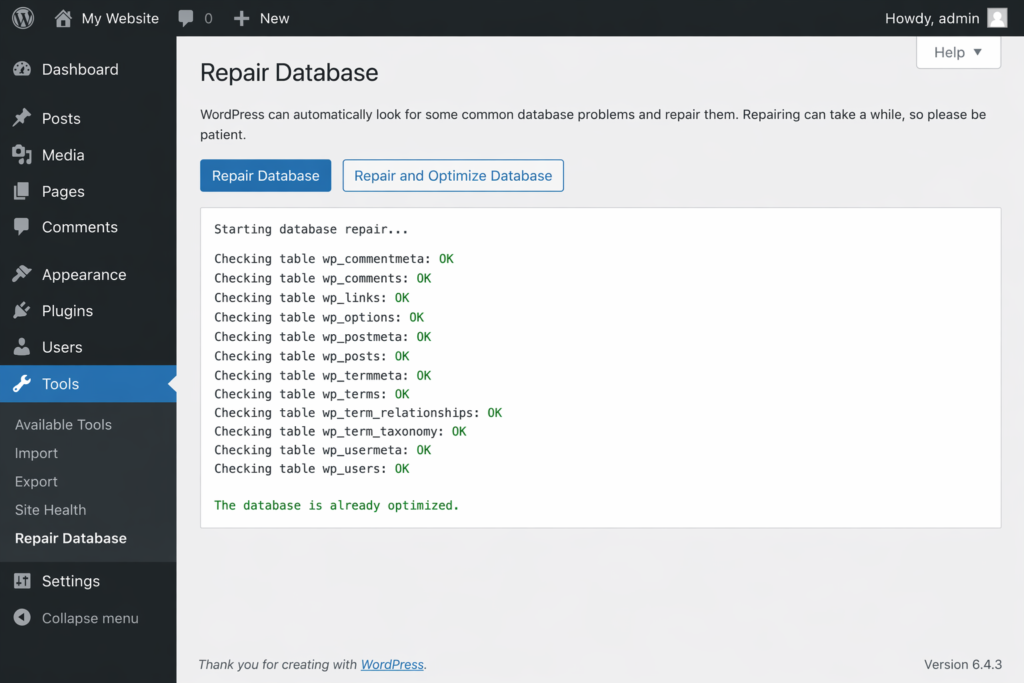
The maintenance page is unauthenticated while WP_ALLOW_REPAIR is set; there is no login wall in front of it, no capability check, no nonce. Anyone who reaches the URL while the define is active can trigger a repair. That is intentional on WordPress’s part; the page needs to work when the database is too damaged for the login flow to complete, but it means the surface cannot be left enabled.
Remove the define(‘WP_ALLOW_REPAIR’, true) line from wp-config.php as soon as the repair completes. Leaving it in place after the repair finishes keeps the unauthenticated access path open, and that is a real exposure, not a theoretical one. The define goes in for the run, the repair executes, and the define comes out.
Repair the WordPress Database in phpMyAdmin
phpMyAdmin repair is the database-native UI path, which runs against the WordPress database via MySQL tooling rather than from inside WordPress itself. Most cPanel, Plesk, and shared-hosting accounts expose phpMyAdmin through a link in the control panel’s database section, and phpMyAdmin exposes a Repair table action on any selection, two clicks away from any table list.
Open phpMyAdmin and select the WordPress database from the left pane. The database name matches the value of DB_NAME in wp-config.php, usually something the installer generated, occasionally a name the site owner chose. The main pane loads the table list for that database: wp_posts, wp_options, wp_postmeta, wp_users, and whatever additional tables plugins and themes have added.
Select the affected tables from the list if the corruption scope is already known from the MySQL error log or from a diagnostic surfaced through WP_DEBUG; select all tables if the scope is not yet known, which is the safer default when the symptom is site-wide rather than isolated to one feature.
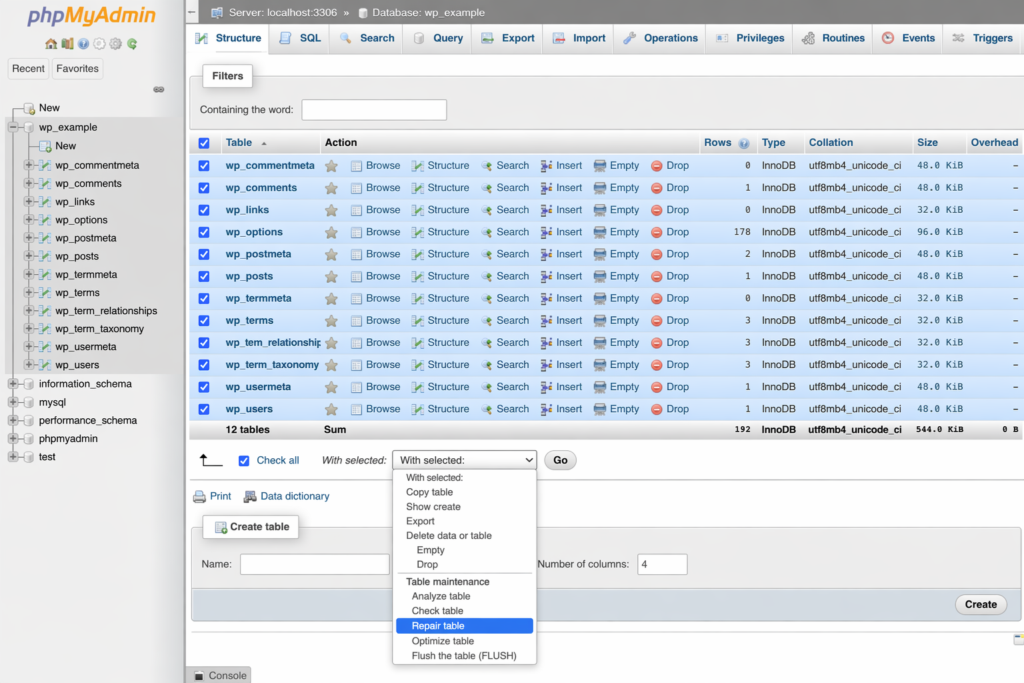
Choose the ” Repair table from the “With selected” dropdown at the bottom of the table list. phpMyAdmin issues REPAIR TABLE against each selected table in turn and returns a per-table status table, one row per table, with the operation’s result for each: OK for tables that repaired cleanly, a warning or error message for tables where the engine had to truncate rows it could not reconstruct, a skip notice for tables the engine cannot touch.
The Optimize table option sits in the same dropdown; the Optimize table action is out of scope for repair and is covered in the separate WordPress database optimization guide.
The MyISAM/ARCHIVE storage-engine constraint applies to phpMyAdmin’s Repair action too. REPAIR TABLE executes against MyISAM and ARCHIVE tables; the engines whose table-level architecture supports the operation, and returns the standard per-table status line, one row per table with an OK, warning, or skip result. When a selected table is InnoDB, phpMyAdmin returns the message “The storage engine for the table doesn’t support repair” for that row, and the table is left untouched.
That is not a repair failure; the engine declines an operation it does not implement. For an InnoDB table that shows corruption, the recovery path is the innodb_force_recovery setting or a restore from the pre-repair backup, neither of which is part of WordPress database repair itself. Where SSH access is available, the shell-level path opens.
Repair the WordPress Database Via WP-CLI
WP-CLI is the command-line repair surface for the WordPress database and is available on any account with SSH access, which covers most managed WordPress hosts, VPS plans, and dedicated setups. From an SSH session in the site’s installation directory, a single command runs the repair:
wp db repairOn sites where the default credentials stored in wp-config.php are overridden or scoped to a separate user, the invocation takes the credential-override flags documented in the WP-CLI reference:
wp db repair --dbuser=<user> --dbpass=<password>Under the hood, wp db repair delegates to mysqlcheck –repair, so the MyISAM/ARCHIVE storage-engine constraint applies here too; the repair lands on MyISAM and ARCHIVE tables, and InnoDB tables are declined at the engine layer rather than repaired. In environments where mysqlcheck is unavailable on the shell, the command falls back to issuing REPAIR TABLE SQL against the database directly, so the same repair still executes through a different transport.
On sites that load custom logic before WP-CLI commands run, the after_wp_config_load hook fires ahead of wp db repair and can influence how the command sees the environment. The full hook reference on developer.wordpress.org is the authoritative source for sites whose bootstrap is non-standard; for a conventional install, the bare wp db repair invocation is sufficient.
Repair the WordPress Database From a Hosting Control Panel
The hosting control panel is the managed-host repair surface for the WordPress database, available on shared hosting and managed WordPress plans that expose a panel UI rather than a shell. Two panel patterns cover most of the market. In cPanel, the MySQL Databases section includes a Repair Database tool; select the database that backs the WordPress install and run the repair from there. In Plesk, the Databases section exposes a Check and Repair operation per database, which executes the same repair against the selected database.
Panel paths vary by hosting provider, and panel UIs change version to version, so the cPanel MySQL Databases and Plesk Databases section labels are the stable anchors rather than any specific click path. For unfamiliar panels, the host’s own documentation is the authoritative source. The repair itself, whichever panel wraps it, ends up issuing the same REPAIR TABLE operation at the database layer, which means the MyISAM and ARCHIVE storage-engine constraint carries through unchanged.
Repair the WordPress Database Using a Plugin
A repair plugin is a WordPress-layer abstraction that runs entirely in wp-admin, with no wp-config.php edit, no phpMyAdmin session, and no shell access required. WP-DBManager is one long-standing practitioner option; it installs from the WordPress plugin directory and exposes a Repair Database action in the plugin UI. Advanced Database Cleaner is another practitioner option that exposes a table-level repair inside its broader cleanup interface.
Because the plugin runs from inside wp-admin on the live site, the pre-repair backup prerequisite carries extra weight for this method: a one-click repair action against a production database is exactly the scenario where a prior export pays for itself. Both plugins also surface cleanup and optimization actions that sit beside their repair controls; cleanup and optimization actions are out of scope for repair and are covered in the separate WordPress database optimization guide.
Whichever method the situation selected, the remaining question is whether the repair actually resolved the corruption it was run against.
WordPress Database Verification After Repair
Verify the WordPress database after repair by running integrity, functional, and behavioral checks in that order. A completed repair is not the same as a confirmed one; the method finishes, the status output reports what it acted on, and the administrator is back at a prompt or a panel screen, but nothing yet has confirmed that the WordPress database actually returned to a functional state. Verification supplies that confirmation across three layers, each aimed at a different risk surface: database integrity at the engine level, WordPress functionality at the admin-area level, and end-user behavior at the level of the flows the site exists to serve.
The database-native confirmation runs CHECK TABLE against the same core WordPress tables the repair acted on and returns a per-table status line in the same shape the repair methods themselves produce. The invocation is direct:
CHECK TABLE wp_posts, wp_options, wp_users;The output lists each table with an op, a msg_type, and a msg_text. An msg_text of OK; the status line the administrator is looking for, confirms the table is healthy and the repair held against that surface. A status of repair-needed, or a msg_type of error naming a residual fault, indicates the table still requires attention; the administrator re-runs the appropriate repair method against the surface the check exposed, rather than assuming the prior pass was complete. CHECK TABLE reads the engine’s own view of table integrity and is the lowest-level confirmation available without re-running the repair itself.
At the WordPress-functional layer, the database must read and write cleanly through wp-admin. The admin area must load without surfacing database errors at the top of the screen, the post and page list views must render their rows, opening a single post or page in the editor must return the content the row holds, and saving a change to Settings → General or any other settings screen must persist without a write-side error.
Each of these is a narrow path through a well-understood table, such as wp_posts behind the post views, wp_options behind the settings save, and wp_users behind the admin-area login itself. The wp-admin spot-check confirms that the database reads and writes those tables the way it did before the corruption surfaced.
At the behavioral layer, the database answers the flows the site is built around, including login on a membership site, search on a content site, checkout on a commerce site, and form submission on a lead-capture site. The flows exercise the database through paths the wp-admin spot-check does not reach, and they are the paths real users will notice first if the repair left a residual problem unaddressed. Exercising one representative flow of each load-bearing kind, end to end, confirms that the WordPress database behaves under the traffic pattern the site actually serves.
A site with a different mix of load-bearing flows tests the flows that matter to it; the point is behavioral coverage, not a fixed checklist.
When all three layers confirm cleanly, OK across the CHECK TABLE output, a working wp-admin spot-check, and green critical user flows, the repair is confirmed on that single site. A production site carries additional discipline on top of the single-incident confirmation.
How to Repair a WordPress Database on a Production Site
Repair a WordPress database on a production site by running the same five methods under a tighter discipline: staging-first execution, an audit trail produced alongside the work, and a clear handoff point when production infrastructure is not in place. The same five methods still apply, and the same verification layers still confirm that the repair held; what changes is the practice that surrounds the repair, a set of controls that contain what happens if the repair is mis-targeted or worsens the corruption, and that produce an artifact the site owner can return to after the incident is closed.
The WordPress database repair runs on a staging clone first, before any action on production. A staging environment is cloned from production, which is a full copy of the production database in a parallel environment that the live site does not depend on, and the repair is attempted on the clone first. If the repair behaves on the clone the way the method’s documented behavior predicts, the validated procedure applies to production with a materially reduced blast radius.
If the repair misbehaves on the clone, truncates rows, surfaces a residual fault the method cannot clear, or produces a status output the administrator cannot interpret, the corruption is diagnosed against the clone rather than against the live site, and production is never touched until a repair path known to work has been established. Most managed WordPress hosts expose a one-click staging clone from their control panel; self-hosted stacks produce the clone with a dump-and-restore against a parallel database. Either shape of staging satisfies the discipline.
The repair produces an audit trail alongside the work. For each repair, the site owner or the acting administrator records what was repaired (which tables, which symptoms), when the work ran (date and time, with time zone), who ran it (named operator, not a shared account), and the before-and-after state (the status output from the failing check, and the OK output from the CHECK TABLE run that confirmed the repair). The audit-trail artifact serves two downstream purposes. Client reporting is the first: a site owner operating on behalf of a stakeholder can hand over a single document that explains what happened to the database and what was done about it, without reconstructing the incident from memory.
Post-incident review is the second: if corruption returns against the same tables weeks later, the audit trail is the baseline the next diagnosis reads against, and the pattern (same tables, same symptom, same cause class) surfaces faster than without the record.
The WordPress database repair handoff to an agency is the scope inflection. A site owner with staging infrastructure and audit discipline already in place runs the production repair in-house and does not need outside help. A site owner without either a staging clone available, no audit-trail artifact produced, and a production incident in progress reaches the point at which production-repair preconditions are absent, and repairing the database directly on production without the surrounding controls is a materially different risk posture than the posture the standard procedure assumes.
A site owner in that position may hand the production repair to an agency with a database-maintenance practice that operates under its own staging and audit controls. IT Monks publishes WordPress database repair guidance and operates a WordPress maintenance practice; the agency handoff is the point at which production infrastructure becomes the determining factor in whether the repair proceeds safely.
A WordPress database returned to a functional state through this work reads and writes cleanly through wp-admin, answers the user flows the site is built around, and clears the engine’s own integrity check against the tables the repair acted on, providing a stable base for the site’s daily operations to run against.
The foundation sibling guide, What is a WordPress database, holds the entity definition under every operation in the cluster; the WordPress database backup guide holds the rollback asset every repair depends on; the WordPress database optimization guide holds the ongoing maintenance the database needs once it is no longer in a repair state.
Contact
Don't like forms?
Shoot us an email at info@itmonks.com




 Gemini
Gemini